The importance of online privacy and security has forced Internet users to take a more cautious approach when using web services. The World Wide Web is far more versatile today than what it was 15 or 20 years ago; but at the same time, there are far more risks and potential threats than ever before.
Hackers and scammers are always lurking around public Wi-Fi networks, so users should take notice and start protecting their assets. These cybercriminals are equipped with the appropriate tools and resources to perform their evil purposes and acts, and one of the newest and most popular modus operandi for cybercrime is cryptojacking.
Bitcoin came up, and after a few years of its road to prominence, it is now the most desirable digital asset in the world. Because of its worth (and that of other cryptocurrencies, as well), hackers see it as an “object of desire” and want to have access to Bitcoin and altcoins at all cost.
Cryptocurrency mining and related costs
Cryptocurrency mining requires several resources that can be costly, such as electricity, equipment (hardware,) and computing or processing power. Cryptojacking refers to the activity of using someone else’s resources to perform cryptocurrency mining, usually without the victim knowing about the issue.
Cryptojacking is the unauthorized use of people’s resources to mine cryptocurrency. It can be performed by a single hacker or a whole organization, and it can affect desktop computers, laptops, smartphones, tablets, IoT devices, and others. Cryptojackers take advantage of people device’s computing power or hash power to solve the required algorithms with the objective of earning crypto rewards in different blockchains.
And, since cryptojacking uses people’s computing and processing capabilities, the devices usually show several signs that make users suspect that something is wrong. Cryptojacking is usually imperceptible at first because it happens when the user is doing any other task in his/her device. However, after a while, the system turns very slow (almost to the point of being unusable), and the battery starts dying really fast, if the gadget is a laptop, smartphone or tablet.
How is cryptojacking performed?
Cryptojacking can be performed by hackers or regular people with the right tools at the right time. The most common places where the phenomenon occurs are public Wi-Fi networks, where nearly everybody can connect and interact. People there usually connect without caring about the possible traces they leave: IP address, login details, and other details. And that’s where cryptojackers pounce.
These people intercept public networks and install malware on the Wi-Fi router, infecting connected computers with the software that performs the illegal and unauthorized crypto mining.
If you have suspicions about your computer being used for illegal crypto mining, leave the network immediately and seek specialized help to take care of your device. But the best you can do is prevent any software from being installed.
How to determine if you have been cryptojacked?
By visiting the website https://cryptojackingtest.com/ you can see if you are the newest victim of the cryptocurrency mining “professionals.” Opera users can enable a built-in ad blocker that offers protection against crypto mining. The website states that four out of five people that run the test gain protection.
What to do?
- Keep your browser up to date: You can always update your browser in the Settings section. After doing it, perform the test once more to ensure protection against crypto jacking. If you encounter any issues at any time, choose a browser that offers the shielding, like Opera.
- Find an antivirus software that has protection: Several cybersecurity companies provide support for cryptojacking attempts. If you don’t know if the brand you use can offer any help, ask the customer service staff.
- Use an extension: Firefox, for example, has an extension called No Coin that can help you deal with these attacks.
The use of a VPN as a protection measure
Virtual Private Networks can encrypt your connection and keep external agents, such as crypto miners, from gaining any information about you, your location and connection. VPNs offer anonymity, and usually, online elements can’t perform attacks to what they can’t see.
Virtual Private Networks implement protocols to create a virtual tunnel, with the intention of sending the user’s information under encryption to remote servers, away from Internet Service Providers, hackers, cybercriminals, malware developers, and crypto miners.
Since they hide the user’s location data and traffic, these tools are also perfect for bypassing censorship, avoiding government surveillance and other situations such as geo-blocking and copyright enforcement, for example.
While they don’t offer 100 percent invisibility, VPNs help you hide your activity and identity in public Wi-Fi networks, making you virtually untraceable. That is why these tools can protect you from cryptojacking because your chances of being affected by infected software are lessened if you encrypt your connection.
TorGuard: the best VPN to avoid cryptojacking
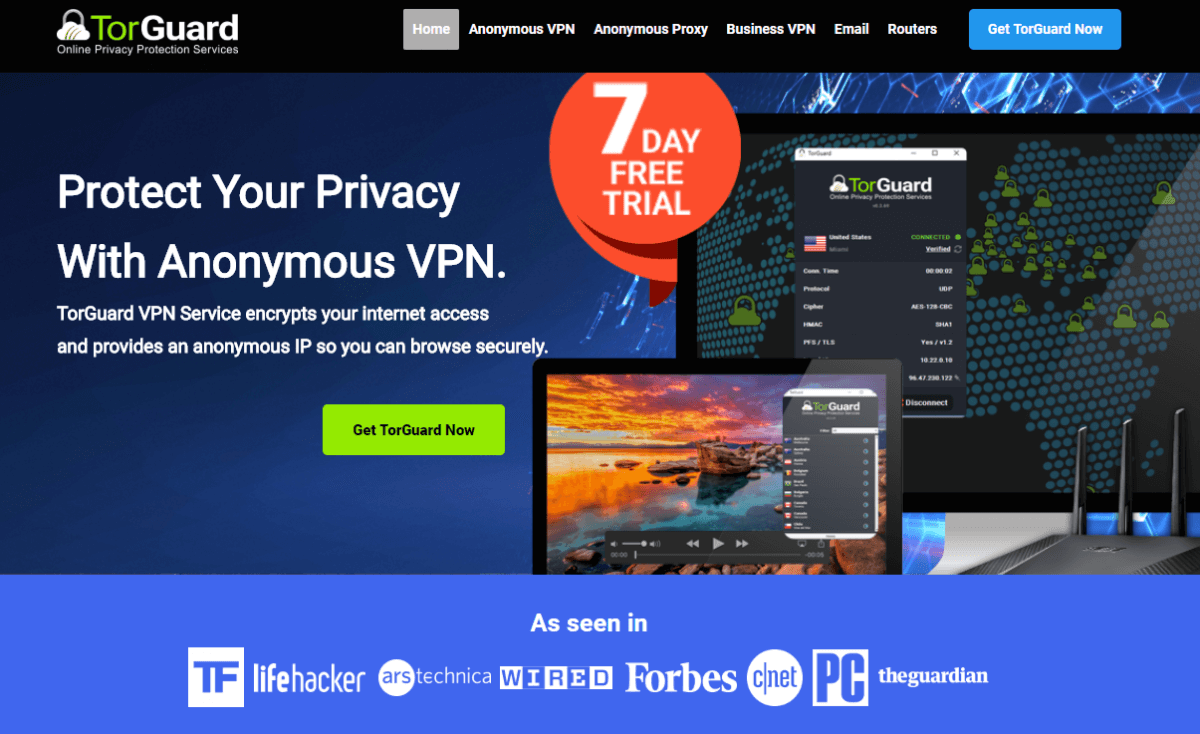
TorGuard is one of the safest and most reliable VPNs in the market. Its security focus will make sure you aren’t affected by cryptojacking: it has DNS leak protection, a full-fledged no-logging privacy policy, a kill switch to disable your Internet connection in the event of a VPN loss, and the military-grade AES 256-bit encryption.
Also, TorGuard has OpenVPN, the best and most secure protocol in the market. Its support staff is highly attentive and responsive and can guide you through the process of knowing more about cryptojacking.
TorGuard offers five simultaneous connections, multiplatform compatibility (including Android, Windows, Mac, iOS, and some routers) and costs $10 per month, a very affordable figure.
How to protect yourself from cryptojacking with a VPN
- Look for a secure VPN brand, like TorGuard
- Go to your device’s app store or to the VPN’s website to download the client
- Install it on your device
- Register for the VPN service
- Log in to your account
- Connect to a VPN server to encrypt your connection
In conclusion, cryptojacking is the act of performing cryptocurrency mining on another person’s device without his or her authorization. It can be a hassle, but fortunately, there are several things you can do to protect yourself, including hiring a VPN service provider.